Shit ransomware virus removal. New locky new .Shit extension.
Locky is back and turns its attention to new file .Shit extension.
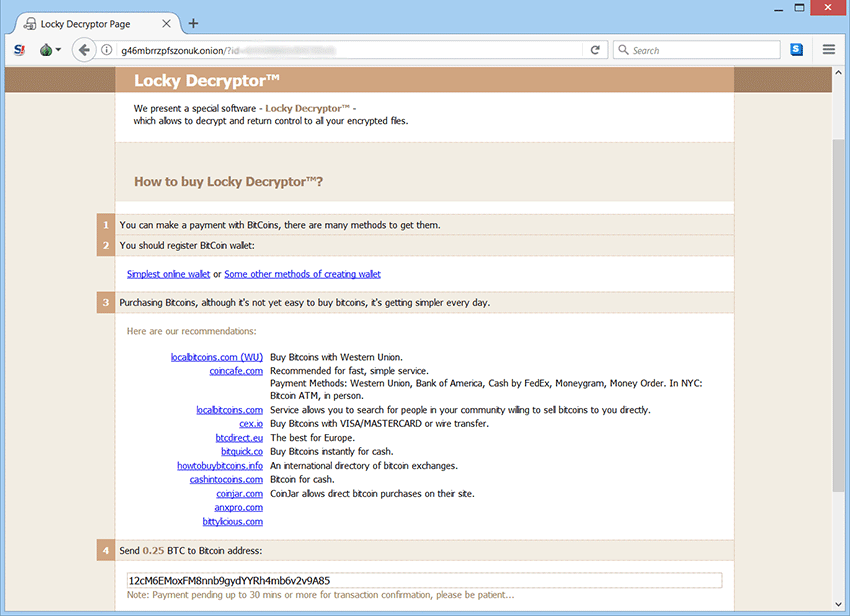
.Shit ransomware decrypt. Ransom note _what_is.
Shit ransomware or .shit extension is the new Locky malware variant that will lock your files and ask you to pay to unlock them. It appears to be related with the new Locky virus, “.shit” extension will be appended. Locky is now following the steps of cerber ransomware and almost every month we report something new from both developers. This was not unexpected, but it was a matter of time that locky campaign will be upgraded, since email providers started to detect Locky attachments as a virus. The new .shit extension comes not long after Locky switches to LNK email file attachments. Unfortunately as of this time the only option to restore locked files is from offline backups of pay what locky asks, however paying is not recommended.
In middle of February 2016 Locky was first discovered and since then it was one of the biggest ransomware campaigns of the year. The name ransomware speaks for itself, as it will encrypted files when victim is infected. Once files are encrypted the virus will demand 0.5 bitcoin (approximately $200) to give users decryption key. AES encryption algorithm will encrypt targeted file after scan of storage drive and network shares. Encryption will no longer allow to open files as you should. To show presence, locky will change the desktop wallpaper with ransom note and also display note in the browser that is used. The note contains of the current situation and what to do to return as it used to be.
Locky checks the local language on the infected computer. System that uses Russian language will not be affected. Lately this ransomware was upgrade and two new campaigns emerged. The new Bart ransomware and the new .zepto locky file extension, .odin extension and not a month later .shit extension. Locky no longer connect remote Command & Control server, instead it is using RockLoader to deliver Bart over HTTPS.
Instead of encrypting the actual files bart will pack them into password protected ZIP archive and append “.bart.zip” extension. However along with bart attack related with locky a new file .zepto and .odin extensions was discovered yesterday. The difference between bought is the price you have to pay. Bart demand $2000, locky demand $200, of course you have to pay in bitcoins. Unfortunately decrypting files for free is unavailable for now.
The new locky and .shit extension also comes with a new ransom note “_what_is.bmp” and “_what_is.html”.
How to protect against ransomware is most frequently asked questions in the past year. Since ransomware has become the biggest threat among all viruses, people ask themselves if there’s a way to protect from such. It is already too late if you once suffered ransom attack and file has been locked. For some there is a solution but for others disappointment. Either way popularity of ransomware rises and new development are presented every day.
What can we do against the battle with ransomware?
- If you are already infected do not pay the ransom! Remove the virus and look for other solutions rather than paying. Paying the ransom may be your only option if you have really valuable data. However we do not recommend doing this because you will support the work of criminals. The risk of losing money and still stuck with encrypted files since there is no guarantee in any way that you will recover what one is lost.
- Security researcher are always working on recovery solutions. Not all ransomware are professionally developed and being cracked, but some are so good developed that there is no current way to be beaten at the current date. One of the solutions is system restore.
- Best solution is if you have a backup, wipe your hard drive and perform system restore. If not, backup your data frequently. Store backup data in any removable storage device or use any online backup services.
- Protect your computer with antivirus, internet security, anti-malware software or new developed applications like anti-ransomware. Highly recommended is to keep it up to date and use the paid surveys. We do not recommend free applications.
Now that you have been infected you have a few options:
Many suggest that you simply pay and hope that you will get all off your data back. However in this case you risk losing money and still being stuck with crypted files. We do not recommend this way simply because you will support the work of hackers and the more money thay get the stronger they will become.
The best option for you is if you have a backup, wipe your hard drive and perform system restore.
Use any type of anti malware software to remove Shit Ransomware.
NOTE: In this option the virus will be removed but the files will remain locked! You have to decrypt your files.
New research discovery shows how ransomware deletes files and substitute encrypted copy of them. It is not guaranteed, but it is a possibility that you may recover your files with data recovery software. Before trying to decrypt any files you can scan your computer for posible data loss.
Go here to find out how to recover deleted files.
Decrypt Shit Ransomware files with .shit extension.
Good news is that we can now use decryption programs. A lot of security companies like Kasperky lab, bitdefender and more has developed a program that is fully capable of decryption key for ransomware malware. You can find this programs anywhere on the internet but it is strongly suggested to download this programs from official websites. NOTE: It may take a long time for your files to be decrypted depending on your PC performance.
- Name – Shit
- Type Spamming – Malware, Ransomware, Trojan Horse
- Danger Level – High
- Brief Description – Encrypt files and demand ransom.
- Symptoms – Poor pc performance or freezing, ransom massages.
- Method – Via Trojan Horse or spam email.
Note: Removing Shit Ransomware manually could be very risky and unpredictable!
To remove this virus we suggest you follow the step by step instructions we provided. Since ransomware virus creates variety of malicious modified registry entries and different files, we strongly advise you to use anti-malware tool. Removing the virus manually requires high computer skills and knowledge.
No Comments Yet