In the vast digital realm, safeguarding one’s online presence is of paramount importance. As our reliance on the internet intensifies, spanning professional communications to personal leisure, ensuring the security of online interactions is crucial. Google Chrome, a globally dominant web browser, is central to these interactions. Its extensive user base makes it an attractive target […]
You are browsing archives for
Author: Val G
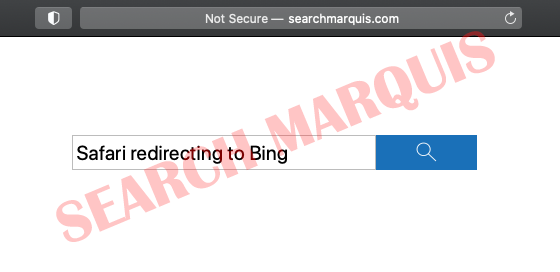
Search Marquis virus removal for Mac
Numerous Mac users are falling victim to a prolific adware strain that reroutes Safari, Google Chrome, and Mozilla Firefox to Bing via SearchMarquis.com. Longevity is a rare trait of adware threats focused on the plaguing computers with macOS on board. Most of these nuisances sink into oblivion mere weeks after being launched. The Search Marquis […]
Milimili virus. How to remove milimili adw...
Milimili is an adware program claiming to be a useful search engine, however ti a malware. Users may consider it as a decent application, but in reality it may compromise user system security. Once computer system is infected with Milimili, user will notice annoying ads popping up frequently. This not only disturbing, but also ads by Milimili may be malicious.
Goldeneye ransomware virus removal.
Goldeneye ransomware was recently spotted to be similar or may be related with Petya and Mischa. As previously spoken that Petya was installing a secondary Mischa ransomware and the malware developers are offering the development as an affiliate service, Goldeneye ransomware seems to be related.
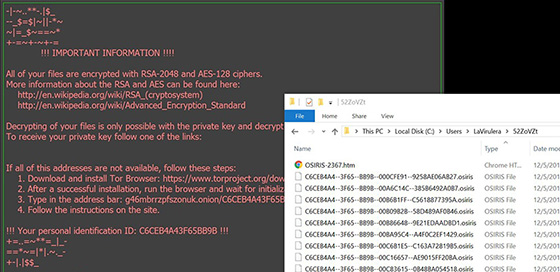
Osiris ransomware virus removal. Decrypt ....
Osiris ransomware or .Osiris extension is part of locky malware. It is considered to be dubbed Osiris ransomawre after the extension, however it is Locky virus. A day after a new .shit extension appended to locked files a new locky variant is reported to append .thor extension, .aesir extension, .zzzzz extension and now .osiris extension.
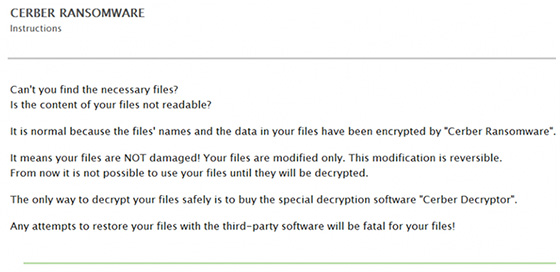
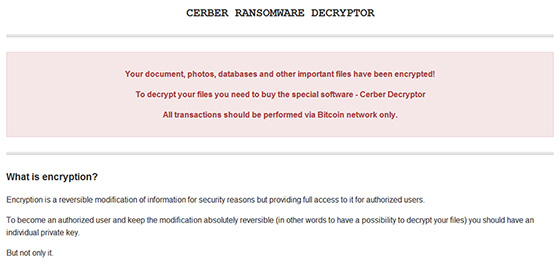
Cerber ransomware back to zero. Note _READ...
Since first reported cerber is one of the best ever developed as of this time ransomware. For the past few months cerber authors have introduced a new variants every single month beginning with .cerber2 extension to .cerber3 and variant with ransom 4char extension along with a new README.hta note. First reports regarding cerber attack were at the beginning of 2016.
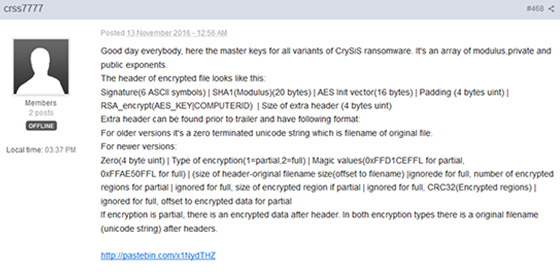
CrySis ransomware master key published. De...
CrySis ransomware master key reported to be published just recently by security researchers, which are working on a decryption tool. This a great news for victims suffered from CrySis rasnomware and .xtbl extension appended to locked files. Is this the end of CrySis projekt or developers are working on a new ransom development.
CerberTear ransomware virus removal. Decry...
CerberTear ransomware is a HiddenTear cerber variant reported to append .cerber extension. It’s called CerberTear Ransomware after the extension .cerber, which is well known and HiddenTear development, what seems to be a combination of two vary famous developments. However there is no relation between cerber and HiddenTear ransomware.
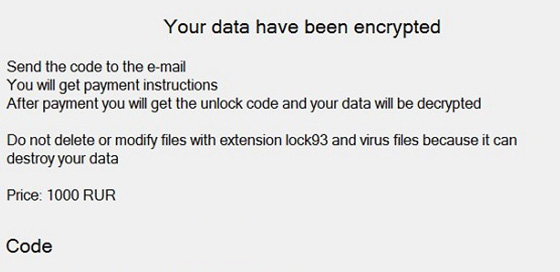
Lock93 ransomware virus removal. Decrypt ....
Lock93 ransomware, the next ransomware on the table reported by MalwareHunterTeam. Ransomware is indeed the most dangerous type of malware, which will encrypt user data and demand a ransom fee in return of decryption key. The name Lock93 comes from the ransom extension appended to victim’s locked files.
Angry Duck ransomware virus removal. Decry...
Angry Duck ransomware, reported by security researcher Michael Gillespie is very dangerous type of malware. It will encrypt user data, generate a RSA key and demand a ransom fee in return of the decryption key. Many dub the ransomwares after the extension appended to locked files, however the name of this one comes from the ransom note image.