Philadelphia Ransomware. New Stampado variant.
Decrypt and remove .locked extension virus.
Philadelphia virus offers Mercy Button called “Give Mercy”.
Philadelphia ransomware is a new variant of Stampado virus. Developer of this malware is named “The Rainmaker” and by the fact that Philadelphia Ransomware is being sold for 400 USD, he wants to offer the apertunity to anyone who wants to be cyber criminal and provide an advanced ransomware into the hands of anyone. Which of course can lead to some custom developments that will not operate accurately and there will be no way for victims to restore locked data, even if they pay. Fabian Wosar Emsisoft security researcher successfully developed decryption tool for Stampado ransomware and all the latest upgrades were also cracked, which really frustrated the malware developer. The Rainmaker end up leaving abusing messages to Fabian hidden in the virus code. Fabian is confident that Philadelphia can also be cracked and decryption tool developed.
Anyway, there have been some reports that The Rainmaker threatens to release Philadelphia Ransomware today and to infect over twenty thousand users on the first day of distribution. The Rainmaker developer revealed some features such as: autodetecting after payment and decrypting automatically, infecting external storage devices. The Rainmaker also threatens that Philadelphia Ransomware is capable of spreading to other computers over the network. The most unusual feature is the Give Mercy button, which will allow particular decryption for free.
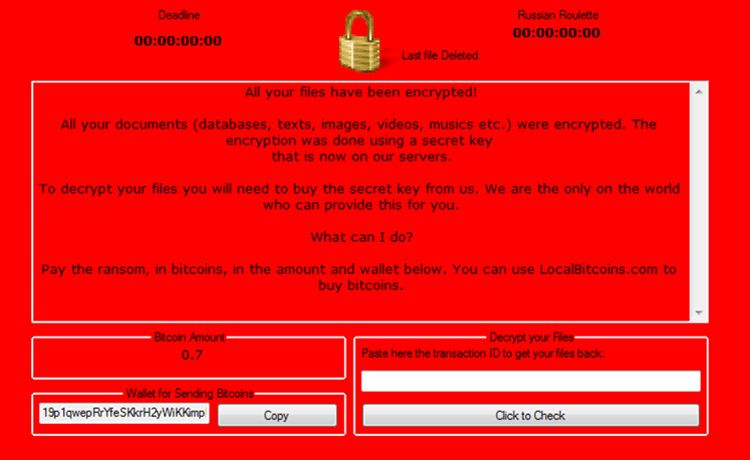
Once computer system is infected Philadelphia ransomware will encrypt user files. The ransom will target all storage devices including removable device, drive root folders and network drives. An RSA encryption key will be generated and stored in developers command and control server. In other to unlock files, victims will have to pay a ransom fee demanded by Philadelphia. Paying is not recommended due to numerous reasons.
Philadelphia targets the following file extensions:
*.7z;*.asp;*.avi;*.bmp;*.cad;*.cdr;*.doc;*.docm;*.docx;*.gif;*.html;*.jpeg;*.jpg;*.mdb;*.mov;*.mp3;*.mp4;*.pdf;*.php;*.ppt;*.pptx;*.rar;*.rtf;*.sql;*.str;*.tiff;*.txt;*.wallet;*.wma;*.wmv;* .xls;*.xlsx;*.zip
After the encryption process finishes, affected files will be renamed with random characters and .locked extension appended. Lock screen will then appear to victim’s desktop, informing them about its presence. The lock screen also contains information on how to pay.
Security researcher also report of a russian roulette option, which if is enabled a counter will begin. When the counter hits zero a a fair amount of files will be deleted. Be aware that decryption tool may be developed, however there is no free solution for this ransomware at this time.
Latest news about Philadelphia ransomware. Fabian succeeded in developing decryption tool. You can now recover locked files for free.
How to protect against ransomware is most frequently asked questions in the past year. Since ransomware has become the biggest threat among all viruses, people ask themselves if there’s a way to protect from such. It is already too late if you once suffered ransom attack and file has been locked. For some there is a solution but for others disappointment. Either way popularity of ransomware rises and new development are presented every day.
What can we do against the battle with ransomware?
- If you are already infected do not pay the ransom! Remove the virus and look for other solutions rather than paying. Paying the ransom may be your only option if you have really valuable data. However we do not recommend doing this because you will support the work of criminals. The risk of losing money and still stuck with encrypted files since there is no guarantee in any way that you will recover what one is lost.
- Security researcher are always working on recovery solutions. Not all ransomware are professionally developed and being cracked, but some are so good developed that there is no current way to be beaten at the current date. One of the solutions is system restore.
- Best solution is if you have a backup, wipe your hard drive and perform system restore. If not, backup your data frequently. Store backup data in any removable storage device or use any online backup services.
- Protect your computer with antivirus, internet security, anti-malware software or new developed applications like anti-ransomware. Highly recommended is to keep it up to date and use the paid surveys. We do not recommend free applications.
Now that you have been infected you have a few options:
Many suggest that you simply pay and hope that you will get all off your data back. However in this case you risk losing money and still being stuck with crypted files. We do not recommend this way simply because you will support the work of hackers and the more money thay get the stronger they will become.
The best option for you is if you have a backup, wipe your hard drive and perform system restore.
Use any type of anti malware software to remove Philadelphia Ransomware.
NOTE: In this option the virus will be removed but the files will remain locked! You have to decrypt your files.
New research discovery shows how ransomware deletes files and substitute encrypted copy of them. It is not guaranteed, but it is a possibility that you may recover your files with data recovery software. Before trying to decrypt any files you can scan your computer for posible data loss.
Go here to find out how to recover deleted files.
Decrypt Philadelphia Ransomware files with .locked extension.
Good news is that we can now use decryption programs. A lot of security companies like Kasperky lab, bitdefender and more has developed a program that is fully capable of decryption key for ransomware malware. You can find this programs anywhere on the internet but it is strongly suggested to download this programs from official websites. NOTE: It may take a long time for your files to be decrypted depending on your PC performance.
- Name – Philadelphia
- Type Spamming – Malware, Ransomware, Trojan Horse
- Danger Level – High
- Brief Description – Encrypt files and demand ransom.
- Symptoms – Poor pc performance or freezing, ransom massages.
- Method – Via Trojan Horse or spam email.
Note: Removing Philadelphia Ransomware manually could be very risky and unpredictable!
To remove this virus we suggest you follow the step by step instructions we provided. Since ransomware virus creates variety of malicious modified registry entries and different files, we strongly advise you to use anti-malware tool. Removing the virus manually requires high computer skills and knowledge.
No Comments Yet