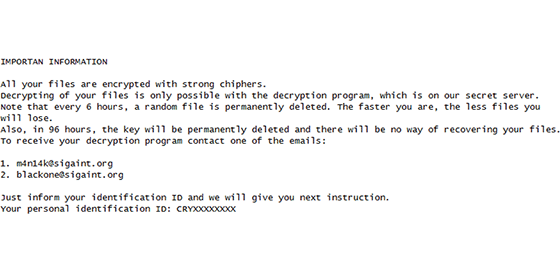
helphomeless@india.com ransomware seems to be а new CrySiS variant. It uses variety of email while infecting users and new variants keep getting reported. The behaviour is similar to all reported variants. Since first discovered CrySiS was not very active, however few months later the activity rising is significant.
You are browsing archives for
Category: Ransomware
CryPy Ransomware. How to remove .cry exten...
CryPy ransomware is new virus discovered by AVG Jakub researcher. It appears that this ransomware is written with Python and use AES-256 to lock a victim’s files. All encrypted files will be renamed to CRY<random characters>.cry. This is also an extension .cry, which will be appended to locked files. A interesting reported by Jakub feature is that CryPy ransomware.
Philadelphia Ransomware. Decrypt and remov...
Philadelphia ransomware is a new variant of Stampado virus. Developer of this malware is named “The Rainmaker” and by the fact that Philadelphia Ransomware is being sold for 400 USD, he wants to offer the apertunity to anyone who wants to be cyber criminal and provide an advanced ransomware into the hands of anyone.
Cerber3 ransomware. How to remove .Cerber3...
Cerber3 ransomware is the latest Cerber development after .cerber2 extension. Previously Cerber was decrypted, however soon after the decryption tool was developed it stopped working due to cerber update. Now we see a constant change of extension. Once “.cerber” later “.cerber2” now “.cerber3” and may be the next will be “.cerber4”.
Crypt0L0cker ransomware virus removal. Dec...
Crypt0L0cker ransomware is new virus substituting the Os with zeros from the genuine cryptolocker ransom name. Apparently this ransomware is the heir of TorrentLocker, with a slight few differences. Both of the ransomwares targets files for encryption in a different way. It is distributed via spam email claiming to be government notices.
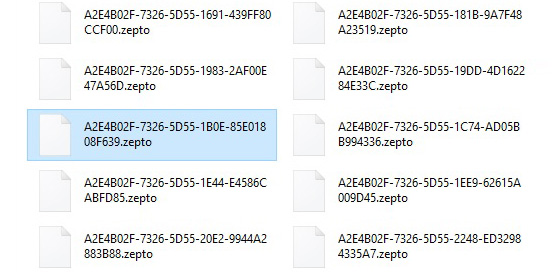
New locky ransomware, new .zepto extension...
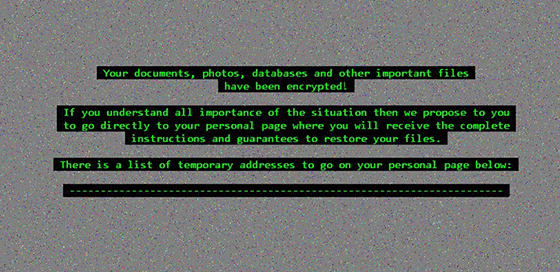
In middle of February 2016 Locky was first discovered and since then it was one of the biggest ransomware campaigns of the year. The name ransomware speaks for itself, it will encrypted files when victim is infected. Once files are encrypted the virus will demand 0.5 bitcoin (approximately $200) to give users decryption key.