Goldeneye ransomware virus removal. High infection rate in germany.
Goldeneye ransomware was recently spotted to be similar or may be related with Petya and Mischa. As previously spoken that Petya was installing a secondary Mischa ransomware and the malware developers are offering the development as an affiliate service, Goldeneye ransomware seems to be related. Furthermore the affiliate program was called Janus, based on a movie criminal organization behind the name Janus Syndicate, which is from the Goldeneye film (James Bond). Apparently Goldeneye ransomware have a high infection rate in germany.
ATTENTION!!!
Since malware virus creates variety of malicious modified registry entries and different files, we strongly advise you to use anti-malware tool. Removing the virus manually requires high computer skills and knowledge.
>>Click here to download free anti-malware removal tool.<<
Upon further inspection the similarities between Petya, Mischa and Goldeneye are obvious. User files will be encrypted after which Goldeneye will restart computer system and pretend to be repairing hard drive due to a failure. Once the fake repair process finish, victims will than be informed with a massage from a flashing skull, however this time is yellow. The worst about this ransomware is that it will prevent users from accessing the computer operating system until payment is done. However paying is not recommended due to numerous of reasons.
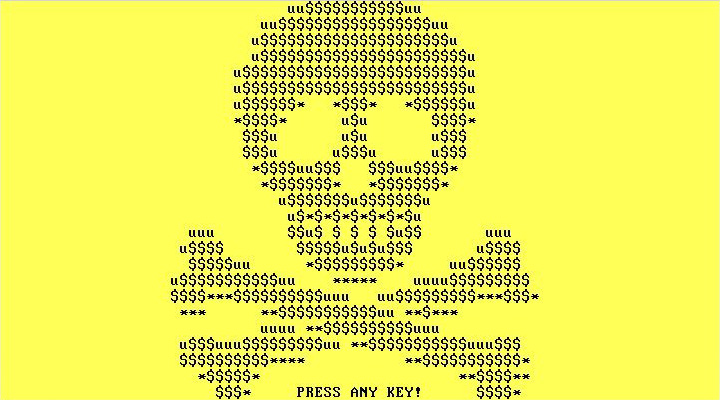
Once user pres any key the massage from Goldeneye will inform victims that Golden eye is responsible for locking the system. The massage also contain information regarding payment. Ransom note “YOUR_FILES_ARE_ENCRYPTED.TXT”.
The note is as follows:
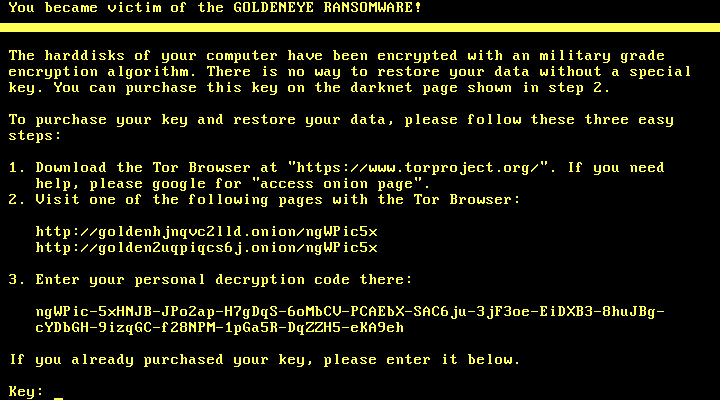
You became victim of the GOLDENEYE RANSOMWARE!
The files on your computer have been encrypted with an military grade encryption algorithm. There is no way to restore your data without a special key. You can purchase this key on the darknet page shown in step 2.
To purchase your key and restore your data, please follow these three easy steps:
1. Download the Tor Browser at “https://www.torproject.org/”. If you need help, please google for “access onion page”.
2. Visit one of the following pages with the Tor Browser:
http://golden5a4eqranh7.onion/[redacted]
http://goldeny4vs3nyoht.onion/[redacted]
3. Enter your personal decryption code there: (redacted)
ATTENTION!!!
Since malware virus creates variety of malicious modified registry entries and different files, we strongly advise you to use anti-malware tool. Removing the virus manually requires high computer skills and knowledge.
Surely you must of heart about ransomware before, if not now you will. Ransomware is malicious attack that will take over control of your files or entire system. This kind of viruses will make victim’s life as stressful as is could get. As mentioned above Goldeneye ransomware is malicious software that will lock you out and then demand money. Goldeneye is an idea behind online fraud strictly designed to generate revenue. When computer users is not protected by some kind of anti malware or antivirus program, opening such attachments will be devastating. Afther virus infiltrate victims system the process of encrypting data will begin. During the process of encrypting which takes time and resources victims may witness poor pc performance, freezing and more weird behavior. The Goldeneye ransomware will appear as a notification message which demands money for key in order to recover access back. Users need to consider purchasing some anti-malware software for own good, also need to consider scaning pc useing any type of anti-malware software to remove the virus.
How to protect against ransomware is most frequently asked questions in the past year. Since ransomware has become the biggest threat among all viruses, people ask themselves if there’s a way to protect from such. It is already too late if you once suffered ransom attack and file has been locked. For some there is a solution but for others disappointment. Either way popularity of ransomware rises and new development are presented every day.
What can we do against the battle with ransomware?
- If you are already infected do not pay the ransom! Remove the virus and look for other solutions rather than paying. Paying the ransom may be your only option if you have really valuable data. However we do not recommend doing this because you will support the work of criminals. The risk of losing money and still stuck with encrypted files since there is no guarantee in any way that you will recover what one is lost.
- Security researcher are always working on recovery solutions. Not all ransomware are professionally developed and being cracked, but some are so good developed that there is no current way to be beaten at the current date. One of the solutions is system restore.
- Best solution is if you have a backup, wipe your hard drive and perform system restore. If not, backup your data frequently. Store backup data in any removable storage device or use any online backup services.
- Protect your computer with antivirus, internet security, anti-malware software or new developed applications like anti-ransomware. Highly recommended is to keep it up to date and use the paid surveys. We do not recommend free applications.
Now that you have been infected you have a few options:
Many suggest that you simply pay and hope that you will get all off your data back. However in this case you risk losing money and still being stuck with crypted files. We do not recommend this way simply because you will support the work of hackers and the more money thay get the stronger they will become.
The best option for you is if you have a backup, wipe your hard drive and perform system restore.
Use any type of anti malware software to remove Goldeneye Ransomware.
NOTE: In this option the virus will be removed but the files will remain locked! You have to decrypt your files.
New research discovery shows how ransomware deletes files and substitute encrypted copy of them. It is not guaranteed, but it is a possibility that you may recover your files with data recovery software. Before trying to decrypt any files you can scan your computer for posible data loss.
Go here to find out how to recover deleted files.
Decrypt Goldeneye Ransomware.
Good news is that we can now use decryption programs. A lot of security companies like Kasperky lab, bitdefender and more has developed a program that is fully capable of decryption key for ransomware malware. You can find this programs anywhere on the internet but it is strongly suggested to download this programs from official websites. NOTE: It may take a long time for your files to be decrypted depending on your PC performance.
- Name – Goldeneye
- Type Spamming – Malware, Ransomware, Trojan Horse
- Danger Level – High
- Brief Description – Encrypt files and demand ransom.
- Symptoms – Poor pc performance or freezing, ransom massages.
- Method – Via Trojan Horse or spam email.
Note: Removing Golden eye Ransomware manually could be very risky and unpredictable!
To remove this virus we suggest you follow the step by step instructions we provided. Since ransomware virus creates variety of malicious modified registry entries and different files, we strongly advise you to use anti-malware tool. Removing the virus manually requires high computer skills and knowledge.
No Comments Yet